OWASP Top 10 pentesting with Penti: Broken Access Control
Broken Access Control is a common and costly threat to web applications. When access control mechanisms don’t enforce proper authorization checks, attackers can gain unauthorized access to accounts, then access restricted resources and exfiltrate data.
Penti’s AI-powered platform delivers broken access control vulnerability testing for companies of any size. Our autonomous agents discover, reproduce, and prioritize real exploitation paths, while our human cyber experts verify impact. With Penti, you get clear evidence and developer-ready remediation.
Broken Access Control: Overview
Why Test for Broken Access Control with Penti’s Agentic AI
Standard pentesting tools flag potential issues but often overlook real access abuse paths that require context, such as chained flows, session management quirks, or nuanced user roles. Penti’s agents behave like a focused red team that understands business logic and access control decisions, connecting the dots from endpoint to exploit to impact.
Rapid scans backed by expert validation
Prioritized Evidence for Fast Remediation

Scalable for Growing Organizations
Simplified Path to Compliance

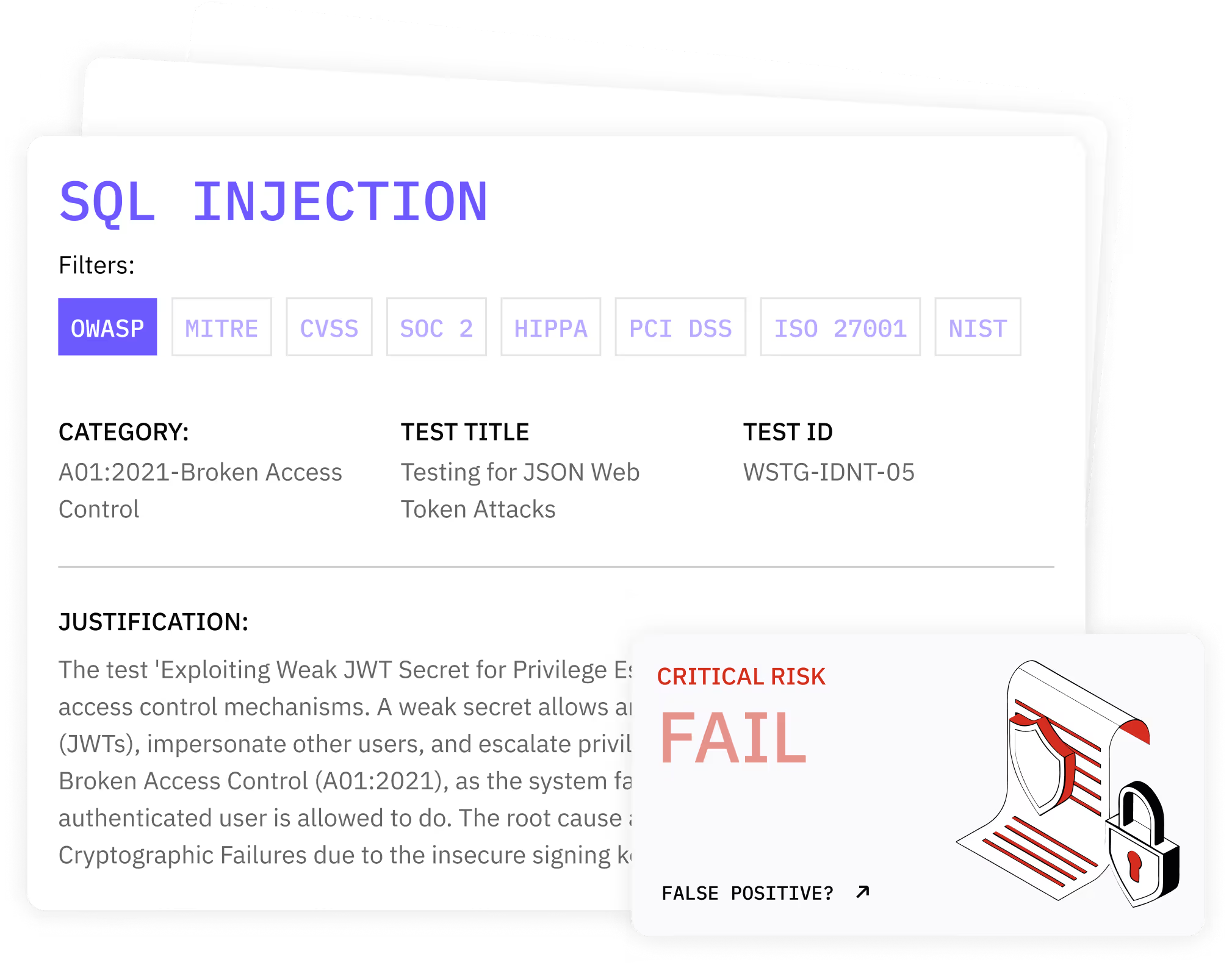
How Penti Detects & Validates Broken Access Control Vulnerabilities
Key features
- Penti maps user roles, object scopes, and access paths across web and API surfaces.
- Safe HTTP request manipulation tests direct object references, parameter tampering, header/cookie variations, and token misuse.
- Privilege escalation checks simulate administrative access and abuse of administrative functions from lower-privileged users.
- Context-aware validation, led by human cybersecurity experts, ties findings to specific objects, tenants, and data types to prove real-world impact.
- Coverage for APIs and SPAs ensures stateful flows and access control mechanisms are tested beyond static pages.
- Penti’s dashboard provides exportable, audit-friendly reports that align findings to controls and provide a defensible testing cadence.
What clients receive
- A verified list of exploitable issues with reproduction steps, PoCs, and guidance for proper authorization checks.
- An executive risk summary that quantifies business impact and prioritizes remediation.
- Evidence artifacts for audits, plus mapped dependencies and affected routes/resources.
- A retest plan with continuous verification to ensure fixes hold as code evolves.
From detection to durable prevention
.svg)
.svg)
.svg)


Trusted by Teams Who Prioritize Real Security
Teams rely on Penti to surface complex access control flaws, and strengthen their security posture quickly. Our AI‑driven platform and expert validation deliver credible results that development, security, and compliance teams trust. See how companies use Penti to prevent access abuse and protect customer data.
FAQ
What vulnerability comes under broken access control?
Broken access control refers to flaws where applications don’t enforce permissions correctly, as in insecure direct object references, missing role checks on endpoints, and weak tenancy boundaries that let users access other users’ resources.
What is the potential impact of broken access control vulnerabilities?
Impacts range from data exposure to account takeover, financial fraud, and operational misuse. Attackers may read or modify sensitive information, trigger privileged workflows, or pivot to administration features.
How does Penti find access control issues that scanners miss?
Our agentic AI models roles, sessions, and object relationships, then performs targeted HTTP request manipulation and parameter tampering across authenticated users to reveal real privilege escalation paths. Our human reviewers validate impact and check findings for false positives.
What does remediation guidance include?
Teams get prescriptive recommendations for authorization checks (controller and middleware), object scoping, tenancy isolation, route protections, secure session management, and safer defaults for access control decisions across the stack.
Can Penti integrate into our SDLC?
Yes. We can run on pull requests, in staging, or against production (with safety throttles). Penti’s findings sync to your tracker with clear ownership and retest workflows.
What’s the difference between horizontal and vertical privilege escalation?
Horizontal privilege escalation lets a user act as a peer (e.g., view another user’s records). Vertical privilege escalation lets a lower-privileged user gain higher privileges (e.g., invoke admin endpoints). Penti tests for both.
-White.avif)
-Color.avif)



